The Cyber Risks Law Firms Are Most Likely to Face (and are least likely to have planned for)

Ask the managing partner of any UK law firm whether cybersecurity is a priority. The answer is almost always yes. The investment is real. The awareness is genuine. The tools are in place.
Ask the IT team whether those tools are consistently enforced, whether the patch windows meet the speed of modern exploitation, and whether the incident response plan has ever been tested against a realistic scenario. The answers tend to be less certain.
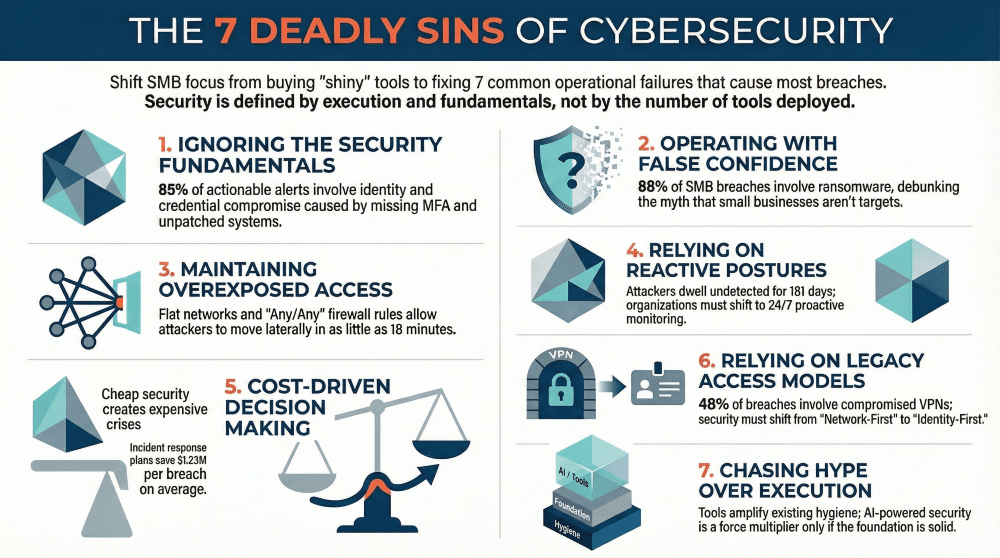
SonicWall‘s 2026 Cyber Protect Report calls this gap “false confidence”. It is, according to their research, one of the most consequential and least discussed problems in cybersecurity. For law firms, where client confidentiality and SRA obligations compound the stakes, it deserves serious attention.
The Attack That Hits Law Firms Hardest: Business Email Compromise
Before addressing the broader security posture, one finding from the SonicWall report warrants immediate attention for any firm handling client funds.
According to Cysurance, a cyber insurance provider and SonicWall partner, 98% of cyber insurance claims stem from Business Email Compromise (BEC) and funds transfer fraud. Not ransomware. A convincing email, a changed payment instruction, and money moved to the wrong account. No credentials stolen. No malware deployed.
For firms managing client account transactions, conveyancing completions, and matter-related payments, this is the attack pattern most likely to result in a claim. The fix is a process control: any change to payment details verified by voice, to a known number, every time without exception.
Three Security Gaps That Underpin Most Breaches
SonicWall’s analysis of breach investigations identifies three failures that appear consistently:
- Weak or missing MFA. 85% of actionable security alerts involve identity, cloud, or credential compromise, according to SonicWall’s 2025 data. For firms where fee-earner accounts hold access to sensitive client matter files, consistent MFA enforcement across all accounts is the baseline control.
- Slow patching. SonicWall found that 61% of exploits are weaponised within 48 hours of a vulnerability being made public. In financial services environments, the average time to patch a high-severity vulnerability is 102 days, according to Gitnux Patch Management Statistics. That is a significant and documented window of exposure.
- Excessive administrative access. More than 3 in 5 cloud compromises investigated by SonicWall traced back to poor access management. When admin accounts carry more access than their role requires, a single compromised credential becomes a firm-wide incident.
ISO27001 and the Controls That Need to Actually Work
For firms maintaining ISO27001 certification, the SonicWall findings are directly relevant. The certification requires demonstrable controls, not assumed ones. SonicWall’s post-incident analysis consistently finds the same pattern: endpoint protection on most devices, not all; logging enabled, but no one reviewing it; backups in place, but never tested.
The gap between documented controls and operational reality is precisely what the certification is designed to surface. A security posture assessment against the actual environment, not the policy documentation, is how firms close it.
What to Do Next
Marlin Communications works with IT Directors and technology leads at UK law firms to assess security posture and address the gaps that matter most. Contact us to arrange a security posture review for your firm.